3rd Tech: A Real-World Guide to What It Means and How to Use It
3rd tech (why this keyword feels confusing—and how I make it simple)
Whenever someone searches 3rd tech, I’ve learned one thing: they want clarity, not a sales pitch.
Because 3rd tech can point to different worlds—IT services, security, sustainability, hardware setups, education tech, even climate innovation networks. And most pages you’ll find online talk only about one world.
So in this article, I’m doing what most people skip: I’ll help you understand what you’re actually looking for, choose the right path, and make smart decisions that save time, money, and stress.
No heavy wording. Just the way I’d explain it to a friend.
What people mean when they say 3rd tech (in plain words)
Here’s my simple definition:
3rd tech is the “third layer” between what you need and the technology you use.
- Layer 1: Your real-life problem (slow work, security gaps, messy handoffs, waste, outdated systems)
- Layer 2: The tools (apps, devices, cloud, networks, platforms)
- Layer 3: 3rd tech (the strategy, setup, integration, support, and standards that make it all actually work)
That’s why two people can type 3rd tech and mean totally different things. One might want IT help. Another might want recycling and data wiping. Another might be researching telecom power systems.
So let’s break it down properly.
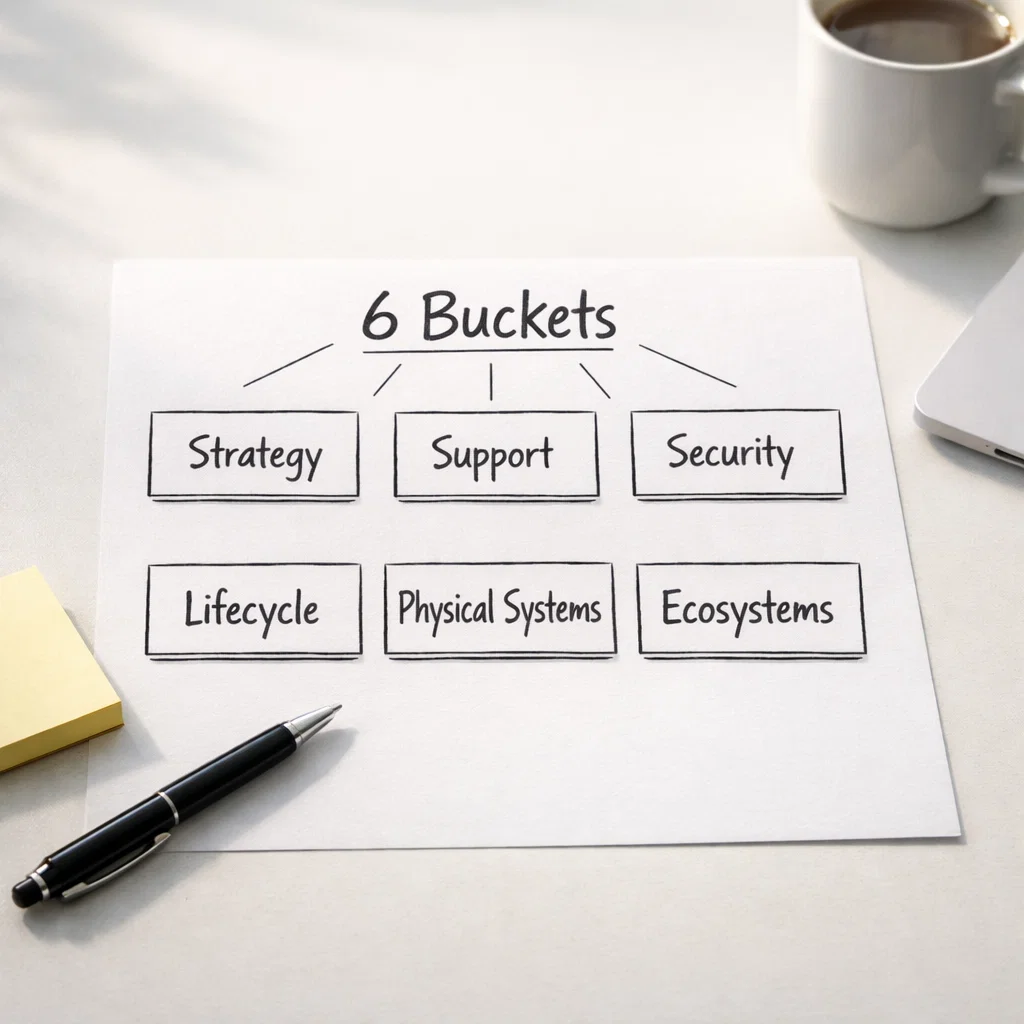
The 6 most common meanings of 3rd tech
1) 3rd tech as IT strategy + vendor selection
This is for teams who are tired of buying tools that don’t fit.
You’re probably in this bucket if:
- You have too many tools and still feel disorganized
- Projects stall because nobody owns the full picture
- You want a clear plan (not another random subscription)
Real-life tip:
Before buying anything new, list the top 5 daily frictions your team complains about. That list is your real roadmap—not vendor marketing.
2) 3rd tech as managed IT + day-to-day support
This is the “keep everything running” side.
You’re probably in this bucket if:
- People message you when Wi-Fi drops or printers act weird
- New staff onboarding takes forever
- Updates, backups, and device health aren’t consistent
Real-life tip:
Ask support providers how they handle “boring” tasks: patching, backups, offboarding, and documentation. That’s where quality shows up.
3) 3rd tech as cybersecurity + risk reduction
This is for organizations that want security to feel steady—not chaotic.
Frameworks like the NIST Cybersecurity Framework 2.0 explain security in outcomes (govern, protect, detect, respond, recover), which helps teams prioritize what to do first. (NIST Computer Security Resource Center)
You’re probably in this bucket if:
- You’re worried about phishing, access control, or cloud misconfigurations
- You need repeatable security habits (not panic mode)
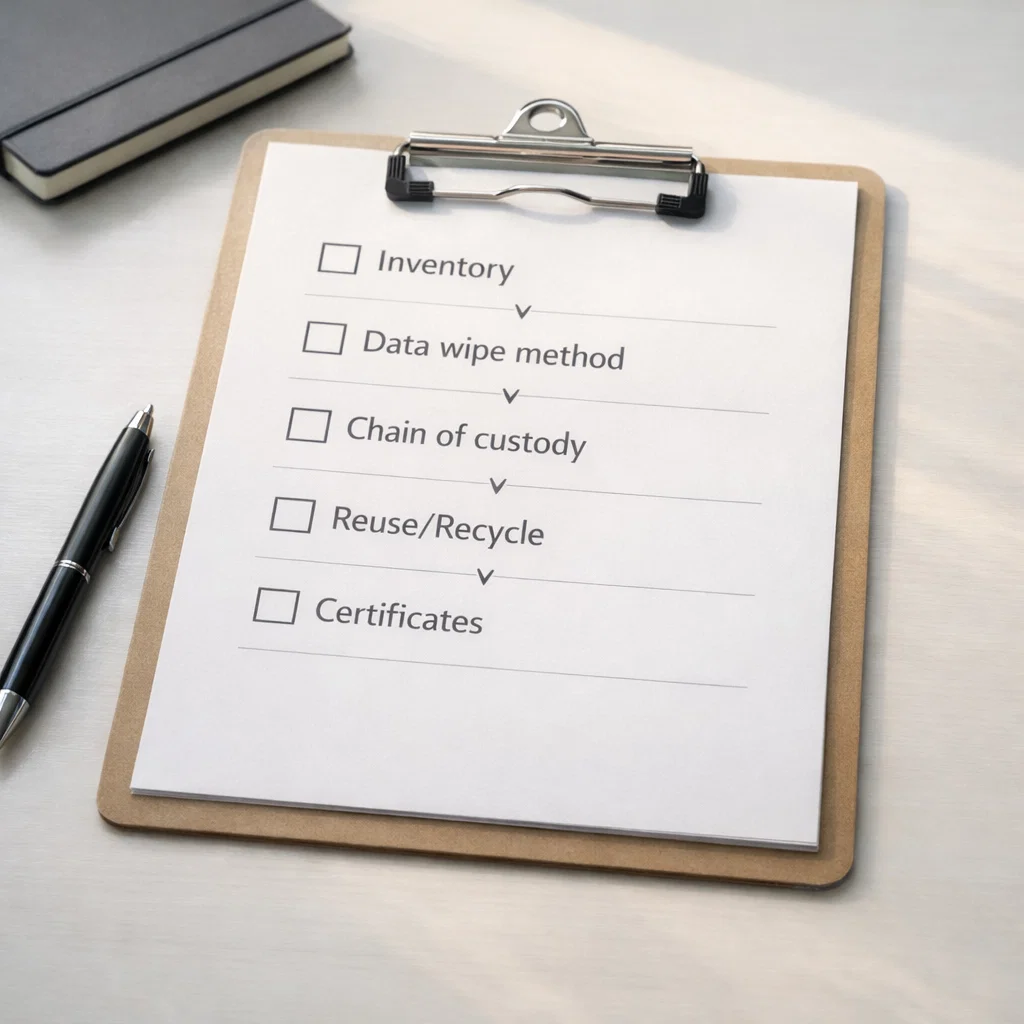
4) 3rd tech as sustainability + IT asset lifecycle (reuse, recycle, disposal)
This is the “what happens after devices are done” side—often ignored until it becomes a mess.
If you deal with end-of-life devices, standards like R2v3 exist to guide responsible electronics reuse/recycling practices.
And guidance like NIST SP 800-88 helps teams make practical media sanitization decisions.
You’re probably in this bucket if:
- Old laptops/drives are sitting in storage “for later”
- Nobody can confidently say what data is on those devices
- You want a clean chain-of-custody process
5) 3rd tech as physical systems (control rooms, display walls, telecom/data center energy)
This bucket is more “hardware + reliability + uptime.”
You’re probably in this bucket if:
- You’re planning a control room, monitoring center, signage, or telecom power setup
- You care about uptime, redundancy, and maintenance planning
Real-life tip:
Don’t judge only by the screen or cabinet. Judge by the service plan: spare parts, warranties, monitoring, and how failures are handled.
6) 3rd tech as ecosystems and innovation networks (especially climate or industry programs)
Some people search 3rd tech while researching networks that help innovations move faster.
These programs usually connect startups/teams with partners, expertise, pilots, and funding paths—so innovation turns into something real.
How to figure out your 3rd tech bucket in 10 minutes
I do this quick exercise all the time:
Step 1: Answer this one sentence
“If 3rd tech works perfectly for me, my life gets easier because ________.”
Examples:
- “we stop duplicating work and reporting becomes simple”
- “we stop worrying about security basics”
- “we dispose devices safely and cleanly”
- “our control room runs reliably and is easy to maintain”
Step 2: Circle your top constraint
Pick one:
- Time (need fast wins)
- Budget (need value per dollar)
- Risk (need security/compliance confidence)
- Scale (need something that won’t collapse later)
That tells you what to prioritize first.
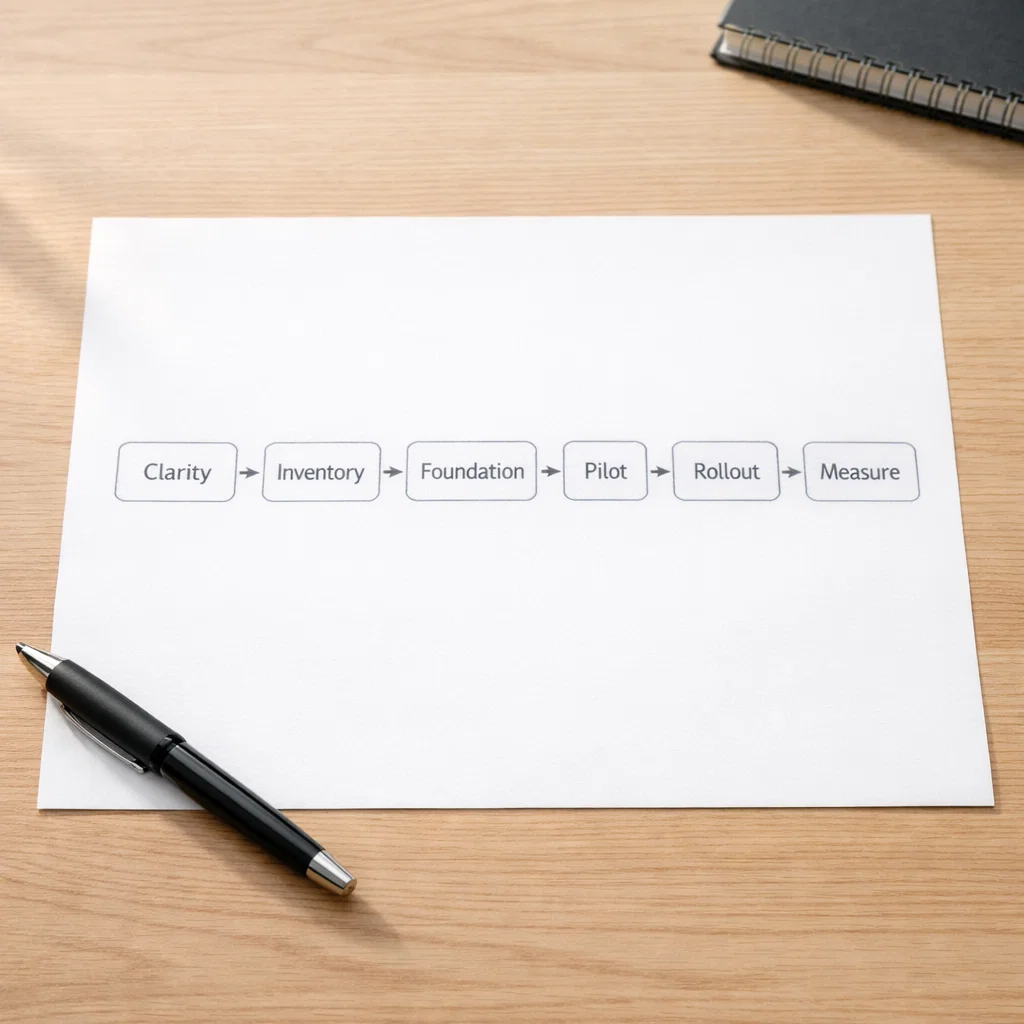
My 3rd tech checklist (the step-by-step that keeps projects clean)
Most competitor-style pages explain what they do. They don’t explain how you should approach it.
This is the part that actually helps readers.
Phase A: Clarity (before you touch tools)
- Write down the top 5 frictions
- Identify what you already pay for
- Decide one measurable goal for the first project
Example goal:
“Cut onboarding time from 10 days to 5.”
or
“Reduce support tickets by 30%.”
Phase B: Inventory (simple and honest)
For businesses, your baseline inventory should include:
- devices (laptops, mobiles, servers)
- accounts + access (who has admin rights?)
- data locations (where are files actually stored?)
- key tools (email, storage, finance, CRM, support)
Phase C: Fix the foundation first
I usually prioritize in this order:
- Identity + access
- Backups + recovery
- Patch/update rhythm
- Visibility/monitoring
- Automation
This aligns nicely with practical security frameworks and control libraries like CIS Controls (commonly used as a baseline).
Phase D: Pilot → rollout → measure
- Pilot with a small group first
- Roll out with short training (simple guides beat long meetings)
- Measure one win and repeat
Security basics for 3rd tech (steady, not scary)
I’m keeping this practical—these are the moves that give the biggest “peace of mind per effort.”
1) Safer sign-ins (password pain is fading)
Passkeys are built on FIDO standards and are designed to move away from “phishable” authentication like passwords and SMS codes.
Real-life tip:
If your team isn’t ready for passkeys everywhere, start with:
- admin accounts first
- high-risk systems (email, finance, cloud dashboards)
- recovery methods documented (so lockouts don’t become chaos)
2) Secure-by-design thinking (even when you’re just buying software)
CISA’s Secure by Design approach pushes the idea that security should be a core business requirement—not a bolt-on.
Real-life tip:
Ask vendors: “What security improvements did you ship in the last quarter?”
If they can’t answer clearly, that tells you a lot.
3) If you run websites/apps, don’t ignore the basics
The OWASP Top 10 is a standard awareness document outlining major web app security risks.
Real-life tip:
Even if you’re not a developer, you can ask your dev team or vendor:
“Which OWASP Top 10 risks are relevant to our app, and what’s our plan for them?”
4) Cloud visibility matters (because cloud sprawl is real)
Cloud Security Posture Management (CSPM) is commonly described as continuously monitoring and helping remediate security risks across cloud environments.
Real-life tip:
Visibility first. Remediation second. If a tool produces noise with no ownership, it won’t stick.
Sustainability + end-of-life: the 3rd tech side people forget
This is where I see teams unintentionally create risk.
The simple problem
Old devices get stored “temporarily,” then forgotten.
That’s how data uncertainty builds.
The clean solution (what good looks like)
- Clear chain of custody
- Documented sanitization method
- Proof (certificates/logs)
- Responsible recycling standards
NIST SP 800-88 describes media sanitization as rendering access to target data infeasible for a given effort level, helping organizations make practical decisions.
R2v3 is a recognized standard in electronics recycling that evolved with industry/regulatory needs.
Global movement around e-waste controls is tightening
The Basel Convention has specific work around e-waste, and there have been amendments affecting how e-waste is listed/controlled.
Real-life tip:
If you’re moving equipment across borders (or using vendors who do), ask where downstream processing happens and how it’s documented.
AI and automation in 3rd tech (helpful when it removes boring work)
I like AI when it makes work lighter—not when it becomes another system to babysit.
Where it usually helps fast:
- summarizing internal notes and tickets
- drafting responses (with a human review step)
- routing support issues
- searching across documentation
- spotting repeat patterns in logs or customer questions
For risk thinking, NIST has an AI Risk Management Framework and a generative AI profile to help organizations manage common risks in a structured way.
Real-life tip:
Any time AI touches customer data, finances, or security decisions—write down:
- what it can access
- what it’s allowed to produce
- who reviews output
- how mistakes are handled
That one page saves a lot of confusion later.
Budget + timeline (what to expect without guessing numbers)
A lot of 3rd tech pages avoid this topic. I won’t.
What usually drives cost
- how messy the current setup is (tool sprawl, unclear ownership)
- security requirements (MFA/passkeys, logging, cloud policies)
- number of users/devices/sites
- how much integration is needed (systems talking to each other)
- documentation + training quality
A realistic rollout rhythm
- Week 1–2: clarity + inventory
- Weeks 3–6: foundation fixes + pilot
- Weeks 7–12: rollout + training + measurement
Real-life tip:
If someone promises a “complete transformation” instantly, ask what they are not doing. The answer usually reveals the truth.
Green flags and red flags (how I judge 3rd tech quality fast)
Green flags ✅
- They start with discovery and outcomes
- They document everything they touch
- They explain trade-offs in simple language
- They propose a pilot, not a giant rollout
- They define what success looks like (metrics)
Red flags 🚩
- Tool-first conversations (“buy this, it fixes everything”)
- No plan for training or adoption
- No offboarding story (what happens when staff leave?)
- No recovery plan (what happens when something breaks?)
- “We’ll handle it” with no documentation
Mini stories (because this is how it looks in real life)
Story 1: The “too many tools” team
They didn’t need new software. They needed:
- one owner for workflows
- fewer tools
- simple automation to remove copy-paste work
Result: faster onboarding and fewer mistakes.
Story 2: The “security feels chaotic” team
They focused on basics:
- cleaner access control
- safer sign-in options (passkeys where possible)
- simple visibility + alerts
Result: fewer urgent fires, more control.
Story 3: The “old devices in storage” team
They built a lifecycle plan
FAQ about 3rd tech
1) What is 3rd tech in simple words?
3rd tech is the practical layer that helps you choose, connect, secure, and run technology so it actually produces results.
2) Why does 3rd tech mean different things to different people?
Because it’s used across multiple industries—IT, security, recycling/lifecycle, hardware systems, and innovation ecosystems.
3) How do I know which 3rd tech direction I need?
Look at your main pain: support, security, integration, device disposal, or physical systems reliability.
4) What should a 3rd tech provider deliver?
A clear plan, documentation, rollout support, and measurable outcomes—not just installation.
5) Is passkey sign-in part of 3rd tech?
It can be, especially when improving authentication and reducing phishing risk—passkeys are based on FIDO standards.
6) What does “secure by design” have to do with 3rd tech?
It helps you choose vendors who treat security as a core requirement, not an afterthought.
7) What’s the first project I should do with 3rd tech?
Start with identity/access cleanup, backup/recovery, or removing the biggest daily friction.
8) Does 3rd tech include e-waste and device disposal?
Yes—device lifecycle planning, sanitization, and responsible recycling are a major part of modern tech operations.
9) What’s one mistake people make with 3rd tech?
They buy tools before they define outcomes and ownership.
10) How do I keep 3rd tech simple?
Pick one measurable goal, pilot with a small group, document changes, then scale.
Helpful external resources (links)
- Passkeys overview (FIDO Alliance) (FIDO Alliance)
- NIST Cybersecurity Framework 2.0 (overview guide) (NIST Computer Security Resource Center)
- OWASP Top 10 (web app security risks) (OWASP Foundation)
- CISA Secure by Design (principles + pledge) (CISA)
- NIST SP 800-88 (media sanitization guidance) (NIST Computer Security Resource Center)
- R2v3 standard overview (SERI) (sustainableelectronics.org)
- Basel Convention e-waste overview + related updates (Basel + EPA) (Basel Convention)
- NIST AI RMF + Generative AI Profile (NIST)






